From Cybersecurity to Physical Steps: Reinforcing Business Safety in an Altering World
In today's swiftly progressing digital landscape, the importance of company safety and security can not be overemphasized. As cyber risks become common and progressively sophisticated, companies should go past traditional cybersecurity actions to protect their properties and operations - corporate security. This is where the integration of physical safety measures comes to be crucial. By integrating the toughness of both cybersecurity and physical security, firms can create a comprehensive protection method that attends to the diverse series of risks they encounter. In this discussion, we will check out the changing danger landscape, the demand to integrate cybersecurity and physical safety, the application of multi-factor authentication steps, the importance of staff member recognition and training, and the adjustment of safety and security procedures for remote labor forces. By examining these essential areas, we will acquire valuable insights into how organizations can reinforce their company protection in an ever-changing globe.
Recognizing the Transforming Danger Landscape
The developing nature of the contemporary world demands a thorough understanding of the altering threat landscape for effective company safety. In today's digital and interconnected age, hazards to business security have actually become much more complex and innovative. As innovation advances and businesses come to be increasingly dependent on digital facilities, the potential for cyberattacks, information breaches, and other security breaches has actually considerably enhanced. It is essential for companies to remain informed and adjust their safety gauges to deal with these advancing dangers.
One trick aspect of comprehending the transforming risk landscape is identifying the different sorts of risks that organizations deal with. Cybercriminals are frequently creating brand-new strategies to exploit vulnerabilities in computer systems and networks. These risks can vary from malware and ransomware attacks to phishing frauds and social engineering strategies. Additionally, physical dangers such as theft, vandalism, and company espionage stay common worries for organizations.
Monitoring and evaluating the threat landscape is vital in order to determine prospective dangers and vulnerabilities. This entails staying updated on the most recent cybersecurity trends, assessing danger knowledge records, and conducting routine danger analyses. By comprehending the changing threat landscape, organizations can proactively apply proper safety steps to mitigate threats and secure their properties, reputation, and stakeholders.
Integrating Cybersecurity and Physical Safety
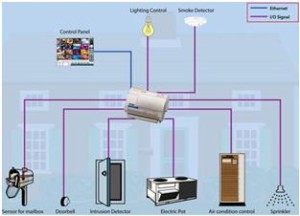
Integrating cybersecurity and physical protection is important for extensive company security in today's interconnected and digital landscape. As companies progressively count on modern technology and interconnected systems, the borders in between physical and cyber threats are ending up being blurred. To successfully secure against these dangers, an all natural method that integrates both cybersecurity and physical safety measures is vital.
Cybersecurity concentrates on protecting electronic assets, such as networks, data, and systems, from unauthorized gain access to, disruption, and theft. Physical protection, on the various other hand, encompasses steps to protect physical assets, people, and facilities from susceptabilities and threats. By integrating these 2 domains, organizations can address susceptabilities and hazards from both physical and digital angles, therefore boosting their overall safety and security pose.
The combination of these 2 techniques enables an extra comprehensive understanding of safety dangers and makes it possible for a unified response to events. As an example, physical gain access to controls can be improved by integrating them with cybersecurity procedures, such as two-factor verification or biometric identification. Similarly, cybersecurity steps can be matched by physical safety and security procedures, such as monitoring electronic cameras, alarm systems, and safe and secure access factors.

Implementing Multi-Factor Authentication Steps
As companies increasingly focus on thorough safety actions, one effective technique is the implementation of multi-factor verification steps. Multi-factor verification (MFA) is a safety and security technique that calls for customers to supply several kinds of identification to access a system or application. This strategy adds an additional layer of security by Full Article incorporating something the individual knows, such as a password, with something they have, like a protection or a finger print token.
By applying MFA, companies can considerably improve their protection pose - corporate security. Traditional password-based authentication has its restrictions, as passwords can be quickly endangered or failed to remember. MFA alleviates these risks by adding an additional verification element, making it harder for unauthorized individuals to get access to sensitive details
There are several types of multi-factor verification approaches readily available, consisting of biometric authentication, SMS-based confirmation codes, and equipment symbols. Organizations need to examine their details needs and select the most proper MFA remedy for their requirements.
Nevertheless, the implementation of MFA need to be thoroughly prepared and carried out. It is critical to strike an equilibrium in between protection and functionality to stop user aggravation and resistance. Organizations should also take into consideration prospective compatibility problems and offer sufficient training and support to make certain a smooth change.
Enhancing Staff Member Recognition and Training
To enhance business security, organizations have to focus on enhancing staff member recognition and training. Many safety and security violations occur due to human mistake or absence of recognition.
Effective employee awareness and training programs must cover a large range of subjects, consisting of data protection, phishing attacks, social engineering, password hygiene, and physical security procedures. These programs must be customized to the certain needs and obligations of various worker functions within the company. Routine training simulations, workshops, and sessions can help employees develop the needed abilities and expertise to recognize and react to safety and security risks efficiently.
In addition, companies must encourage a society of safety recognition and supply continuous updates and reminders to maintain employees notified regarding the most up to date hazards and mitigation methods. This can be done with internal interaction channels, such as newsletters, intranet portals, and e-mail projects. By fostering a security-conscious workforce, companies can dramatically minimize the likelihood of protection occurrences and safeguard their valuable possessions from unapproved gain access to or compromise.

Adapting Safety Actions for Remote Workforce
Adjusting company safety and security procedures to suit a remote labor force is important in making certain the protection of delicate info and possessions (corporate security). With the raising fad of remote work, organizations must execute proper protection actions to mitigate the risks connected with this new method of working
One important element of adapting safety procedures for remote work is establishing secure communication channels. Encrypted messaging platforms and digital exclusive networks (VPNs) can assist safeguard sensitive information and avoid unauthorized accessibility. In addition, companies must implement click here to find out more the usage of strong passwords and multi-factor authentication to enhance the safety and security of remote access.
An additional essential consideration is the implementation of secure remote accessibility options. This involves providing staff members with safe access to company resources and data via online desktop computer framework (VDI), remote desktop protocols (RDP), or cloud-based remedies. These technologies guarantee that sensitive info stays protected while making it possible for workers to execute their roles effectively.

Finally, thorough protection recognition training is vital for remote staff members. Training sessions must cover finest techniques for firmly accessing and handling sensitive information, determining and reporting phishing efforts, and keeping the total cybersecurity health.
Final Thought
In conclusion, as the risk landscape continues to advance, it is vital for organizations to strengthen their safety determines both in the cyber and physical domains. Incorporating cybersecurity and physical protection, executing multi-factor authentication actions, and improving employee recognition and training are essential actions in the direction of achieving durable corporate protection.
In this discussion, we will check out the changing hazard landscape, the need to integrate cybersecurity and physical safety, the implementation of multi-factor verification measures, the relevance of employee recognition and training, and the adaptation of protection procedures for remote labor forces. Cybersecurity steps can be complemented by physical protection steps, such as security cameras, alarm systems, and safe and secure access factors.
As organizations progressively focus on comprehensive security procedures, one reliable method is the application of multi-factor verification measures.In conclusion, as the danger landscape proceeds to evolve, it is vital for companies to reinforce their protection measures both in the cyber and physical domain names. Incorporating cybersecurity and physical protection, applying multi-factor verification actions, and boosting staff member awareness and training are necessary actions towards achieving robust corporate safety and security.